Leverage frameworks for cybersecurity improvement
According to Gregory J. Skulmoski, author of Shields Up: Cybersecurity Project Management, the cornerstone of any compliance program is quality management. Skulmoski quotes from the Information Technology Infrastructure Library (ITIL) that “continuous improvement is fundamental to providing services valued by the end-user and is maximized if a continual improvement mindset is adopted by all project stakeholders.”1
The National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF), Center for Internet Security (CIS) Critical Security Controls, and the Health Insurance Portability Act of 1996 Security Rule are examples of common frameworks that define the “what” for cybersecurity. Each framework defines controls and risk—the “why”—for organizations.
The Department of Health & Human Services’ Health Insurance Portability and Accountability Act (HIPAA) Security Series includes additional notes and follow-up questions that provide additional guidance on the importance of such controls. For example, in Security Standards: Physical Safeguards - Contingency Operations, the guide provides clarifying questions that speak to the importance of controls, such as:
- Are procedures developed to allow facility access while restoring lost data in the event of an emergency, such as a loss of power?
- Do the procedures identify personnel that are allowed to reenter the facility to perform data restoration?2
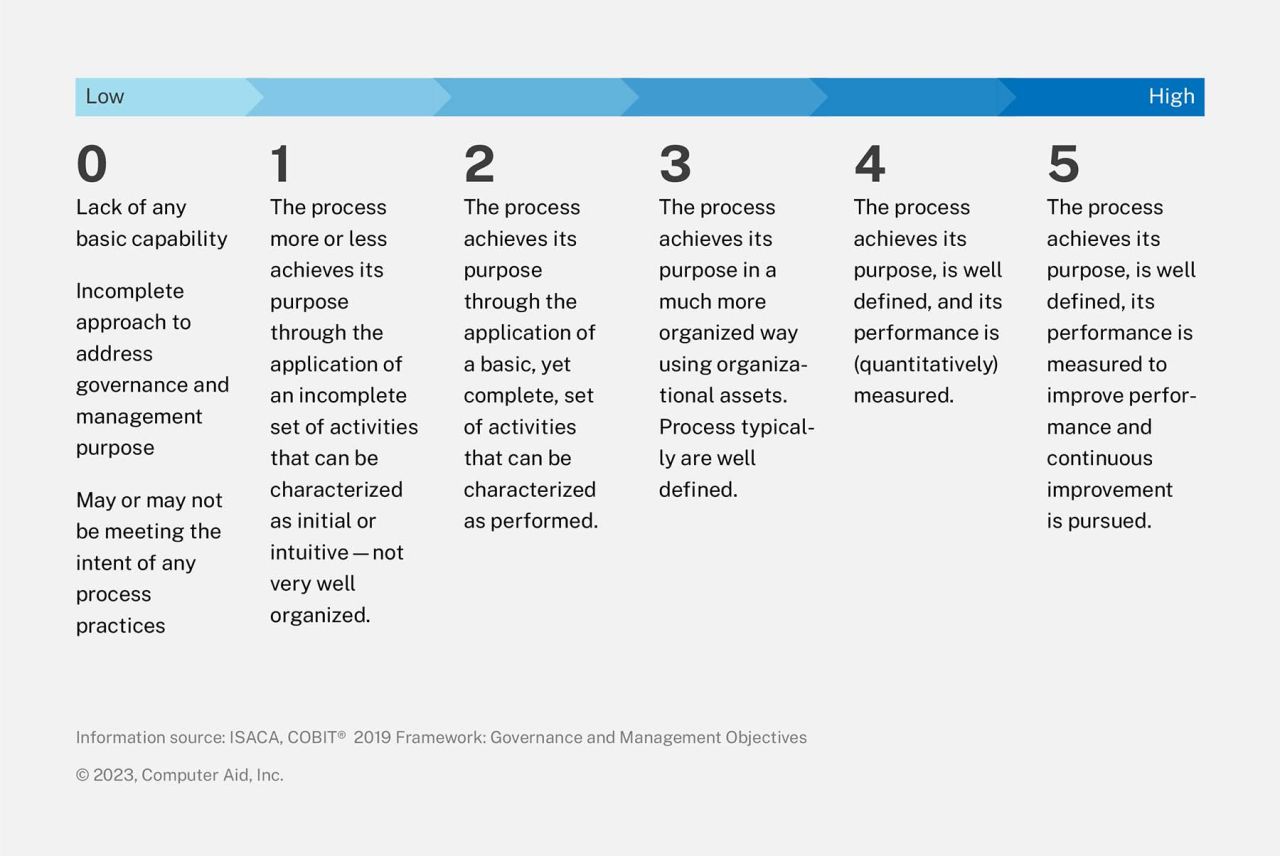
In addition to these frameworks, the use of maturity models allows organizations to measure their controls against standards. While these standards are mostly focused on the design and implementation of security processes, they also include elements of process interdependencies and organizational governance. The following diagram demonstrates the basic structure of ISACA’s COBIT capability levels; this is one of the most commonly used standards for cybersecurity assessments.
Organizations can leverage the security framework(s) that best fit their needs and assess their controls against implementation standards. This begs the question, “Why do so many organizations continue to struggle with improving their long-term cybersecurity posture?”
According to CEO Views, here are the top six reasons for cybersecurity failures:
Build a comprehensive cybersecurity improvement plan
While the frameworks and implementation standards do a reasonable job of defining the “What” and “Why” of cybersecurity, they do not provide actionable information on the “How.” Questions that arise may include:
- How do we get our senior and cybersecurity leaders aligned?
- How should our overall organizational strategy account for cybersecurity?
- What do my customers and other stakeholders expect and need from us in terms of cybersecurity?
- How do we know if we are getting any better?
- How do we build, train, and maintain a workforce for the future?
- How do we design, manage, and improve our cybersecurity work processes?
- How do we measure and report on results?
What leaders need is a systems perspective; examining how an organization can leverage its resources, culture, values, and operations to deliver measurable cybersecurity improvement results. Organizations should look to apply their existing knowledge of strategic planning, process reengineering, quality assurance, and program/project management. NIST provides an option for this.
The Baldridge Cybersecurity Excellence Builder (BCEB) v 1.1 is a self-assessment tool to help organizations better understand the effectiveness of their cybersecurity risk management efforts and identify improvement opportunities in the context of their overall organizational performance.5 This product is derived both from the NIST CSF and the Baldridge Performance Excellence Program. The Baldridge Performance Excellence Program is designed to accomplish the following:
- Raise awareness about the importance of performance excellence in driving the U.S. and global economy
- Provide organizational assessment tools and criteria
- Educate leaders in businesses, schools, health care organizations, and government and nonprofit agencies about the practices of best-in-class organizations
- Recognize national role models and honor them with the only Presidential Award for performance excellence, the Malcolm Baldridge National Quality Award
The BCEB enables organizations to not only assess cybersecurity efforts, but also understand a systems or enterprise-wide view of the organization to better ensure that improvement measures are efficient, effective, and maintainable. The BCEB provides a comprehensive view that assesses multiple elements of the cybersecurity improvement process.6
For example, critical infrastructure is one of the primary concerns of the Federal Government and most recently outlined in the National Cybersecurity Strategy. The relationship between the BCEB and the Framework for Improving Critical Infrastructure Cybersecurity can be shown through the use of their self-assessment tool. Features of both the BCEB and Framework are reflected in the self-assessment tool and other supplemental resources offered available through NIST.
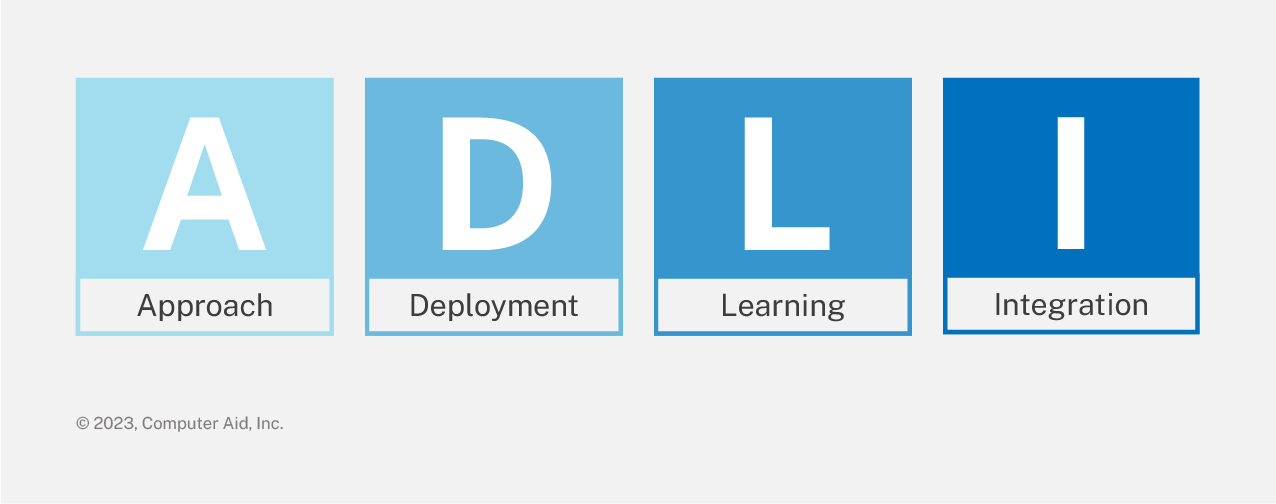
The BCEB includes questions about the organization, not just cybersecurity practices. NIST considers cybersecurity to be an organization-wide concern. The BCEB and supporting toolsets are not meant to replace existing security frameworks, but rather to leverage specially designed assessing processes, listed below (“ADLI”), against the elements of the organization’s cybersecurity-related processes:
- Approach: How do you accomplish your organization’s cybersecurity-related work? How systematic are the key processes you use?
- Deployment: How consistently are your key cybersecurity-related processes used in relevant parts of your organization?
- Learning: How well have you evaluated and improved your key cybersecurity-related processes? How well have improvements been shared within your organization?
- Integration: How well do your cybersecurity-related processes address your current and future organizational needs?7
Organizations that complete a BCEB assessment and integrate the guidance into their overall GRC programs and cybersecurity management efforts can expect both tangible and intangible benefits. To learn more about how the BCEB can be used to improve your cybersecurity programs, NIST has provided a recorded webcast that provides more information on the purpose of the BCEB and a Lessons Learned session provided by University of Kansas Medical Center.8
CAI provides the IT security consulting services that can help local governments, businesses, and organizations assess their security posture and begin the process of building an IT security governance program. Arrange a meeting with our experts to assess your vulnerabilities and get ahead of cyber threats.
Endnotes
- Skulmoski, Gregory J. Shields up: Cybersecurity Project Management. New York, NY: Business Expert Press, 2022. ↩
- “Security Physical Safeguards.” Department of Health and Human Services, March 2007. https://www.hhs.gov/sites/default/files/ocr/privacy/hipaa/administrative/securityrule/physsafeguards.pdf. ↩
- “Building a Maturity Model for COBIT 2019 Based on CMMI.” ISACA. ISACA, December 2021. https://www.isaca.org/resources/isaca-journal/issues/2021/volume-6/building-a-maturity-model-for-cobit-2019-based-on-cmmi. ↩
- “Cybersecurity Failures: Top 6 Reasons.” CEO Views. The CEO Views, September 9, 2020. https://theceoviews.com/top-6-reasons-for-cybersecurity-failures. ↩
- “Baldrige Cybersecurity Initiative.” NIST. National Institute of Standards and Technology, October 25, 2021. https://www.nist.gov/baldrige/products-services/baldrige-cybersecurity-initiative. ↩
- “About Baldrige.” NIST. National Institute of Standards and Technology, October 7, 2021. https://www.nist.gov/baldrige/how-baldrige-works/about-baldrige. ↩
- “Baldrige Cybersecurity Excellence Builder.” NIST. National Institute of Standards and Technology, March 2019. https://www.nist.gov/system/files/documents/2019/03/24/baldrige-cybersecurity-excellence-builder-v1.1.pdf. ↩
- “Baldrige Cybersecurity Excellence Builder Training.” NIST. National Institute of Standards and Technology, January 21, 2021. https://www.nist.gov/baldrige/baldrige-cybersecurity-excellence-builder-training. ↩




